Threat Watch vs Zignt
Side-by-side comparison to help you choose the right product.
Threat Watch
Instantly assess your cybersecurity health with a free scan for critical vulnerabilities.
Last updated: March 1, 2026
Zignt automates secure contract signing with reusable templates for fast, compliant, and hassle-free transactions.
Last updated: March 1, 2026
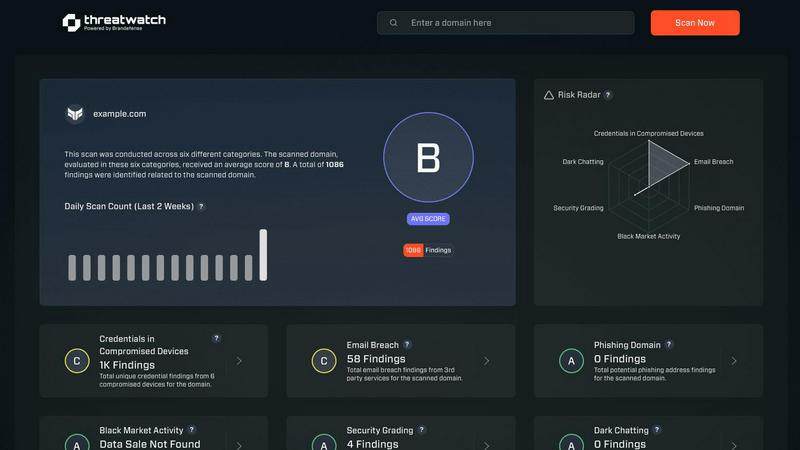
Visual Comparison
Threat Watch
Zignt

Feature Comparison
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch provides a unified, real-time dashboard that evaluates an organization's overall cybersecurity posture. It systematically scans and analyzes multiple critical security categories, delivering a clear and consolidated view of risks. This holistic assessment transforms disparate data points into an understandable security health score, enabling teams to quickly grasp their current standing and identify areas requiring immediate attention.
Automated Compromised Credentials Detection
The platform continuously monitors data breaches and leak repositories to identify if employee credentials, such as emails and passwords, have been exposed. This automated surveillance extends beyond public databases to include dark web sources, ensuring that stolen login information is flagged promptly. This allows security teams to enforce password resets and implement multi-factor authentication before accounts can be abused.
Breached Account and Phishing Risk Monitoring
Threat Watch actively tracks instances where corporate email accounts appear in known data breaches or are being used in phishing campaigns. It identifies if company domains are being spoofed or impersonated, alerting organizations to active phishing threats targeting their employees or customers. This early warning system is crucial for preempting social engineering attacks and protecting brand reputation.
External Attack Surface Analysis
The solution automates the discovery and assessment of an organization's externally visible digital assets, including domains, IP addresses, and associated services. It identifies misconfigurations, outdated software, and unintended exposures that could serve as entry points for attackers. This continuous mapping provides a clear picture of the external attack surface, enabling proactive hardening of defenses.
Zignt
Create Reusable Templates
With Zignt, users can create contract templates that can be reused indefinitely. This feature allows businesses to add date fields, text boxes, and signature blocks to their PDFs in just minutes. Once a template is configured, it can be sent out multiple times without the need to recreate the same contract, saving valuable time and effort.
Seamless Sharing Options
Zignt provides flexible sharing options to send contracts effortlessly. Users can deliver contracts via email, complete with automated reminders, or share a unique Zignt Link that functions similarly to payment links. This feature ensures that contracts are easily accessible and can be signed without unnecessary delays, enhancing the overall user experience.
Instant Signing and Delivery
Once all parties have signed the contract, Zignt automatically sends the executed PDF to everyone involved via email. Each document is accompanied by compliance data to ensure legal protection. The automatic inclusion of essential details, such as IP addresses, timestamps, and signer identities, guarantees a thorough audit trail for every contract.
AI-Powered Renewal Tracking
Zignt's intelligent AI technology tracks contract renewal dates automatically, sending smart reminders to users before contracts expire. This proactive feature eliminates the need for manual tracking, allowing businesses to stay ahead of critical deadlines and manage their agreements more effectively.
Use Cases
Threat Watch
Proactive Risk Management for IT Security Teams
Security operations and IT teams use Threat Watch to shift from a reactive, alert-driven model to a proactive risk management stance. By having a centralized, real-time view of external threats like compromised credentials and dark web exposures, teams can prioritize remediation efforts based on actual risk, allocate resources more effectively, and prevent incidents before they escalate into full-scale breaches.
Compliance and Audit Readiness
Compliance officers and auditors leverage the platform to demonstrate due diligence in monitoring third-party and digital risks. The comprehensive reports and historical data provided by Threat Watch serve as evidence of continuous security monitoring, helping organizations meet regulatory requirements for data protection, risk assessment, and incident response preparedness across various frameworks.
Executive and Board-Level Security Reporting
Business leaders and board members utilize Threat Watch's clear, dashboard-driven insights to understand the organization's cyber risk in business terms. The platform translates technical vulnerabilities into prioritized business risks, facilitating informed decision-making regarding security investments and providing assurance that the digital attack surface is being actively managed.
Vendor and Third-Party Risk Assessment
Organizations extend their security monitoring to assess the cyber health of key partners and vendors. By analyzing the external digital footprint of third parties, businesses can identify if a supplier's breached data or exposed assets pose a downstream risk to their own network, enabling more informed vendor risk management and contract discussions.
Zignt
Startups Streamlining Onboarding
Startups can utilize Zignt to streamline their onboarding process by creating and sending employment contracts efficiently. With reusable templates and automated reminders, hiring managers can ensure new hires receive their contracts promptly, enhancing the onboarding experience.
Legal Teams Managing Multiple Contracts
Legal teams can benefit from Zignt by managing multiple contracts simultaneously. The platform's collaboration features enable team members to work together on contract preparation while maintaining control over permissions and access, ensuring that sensitive information is protected.
Sales Departments Accelerating Deals
Sales departments can leverage Zignt to accelerate their deal-closing process. By utilizing reusable templates and instant signing capabilities, sales representatives can send contracts to clients quickly, reducing the time it takes to finalize agreements and proceed with business operations.
Vendor Management Simplified
Companies managing vendor relationships can use Zignt to simplify the contract lifecycle with suppliers. With AI-powered renewal tracking and automated reminders, businesses can stay organized and ensure that vendor contracts are renewed on time, preventing service interruptions.
Overview
About Threat Watch
Threat Watch is a unified cybersecurity intelligence platform designed to provide organizations with a comprehensive and real-time view of their digital security posture. It functions as a centralized hub for cyber health assessment, continuously analyzing an organization's external digital footprint, assets, vulnerabilities, and exposures. The platform's core mission is to transform complex, fragmented threat data into a clear, actionable picture of risk. By automating the discovery and assessment of critical security categories, Threat Watch empowers IT security teams, compliance officers, and business leaders to move from reactive defense to proactive risk management. Its primary value proposition lies in its speed and clarity; it rapidly identifies issues like compromised credentials, breached accounts, phishing risks, and dark web exposures, allowing teams to prioritize and mitigate threats faster than traditional manual methods. It is ideally suited for businesses of all sizes seeking to understand their external attack surface and strengthen their defenses against evolving cyber threats. The platform's "Uncover your Cyber Security Health, Fast!" approach delivers immediate insights, enabling organizations to take swift, informed action to secure their digital perimeter.
About Zignt
Zignt is a cutting-edge contract management and electronic signature platform designed to revolutionize the way businesses handle their agreements. By simplifying the traditionally slow and cumbersome process of contract creation, sending, and tracking, Zignt enables organizations to accelerate their workflows without compromising on legal compliance or security. This platform caters to a wide range of users, from fast-growing startups to well-established enterprises, all of whom require a swift and effective means of managing contracts. Zignt's core value proposition lies in its elimination of per-signature fees, which provides a predictable and scalable pricing model. With features like reusable contract templates, unlimited document signatures, and seamless collaboration tools, Zignt empowers teams to operate efficiently. Its intelligent functionalities, such as AI-powered renewal tracking and automated reminders, significantly reduce manual effort, prevent missed deadlines, and offer full visibility into the entire contract lifecycle. The combination of bank-level security, compliance with international legal standards, and an intuitive user interface positions Zignt as a trusted solution for teams around the globe, enabling them to get contracts signed in minutes rather than days.
Frequently Asked Questions
Threat Watch FAQ
What does Threat Watch actually scan and monitor?
Threat Watch performs a non-intrusive external scan of your organization's digital footprint. It monitors for compromised employee credentials in data breaches, detects corporate accounts involved in phishing schemes, identifies exposed company data on the dark web, and analyzes publicly accessible assets for vulnerabilities. It does not require internal network access or agents installed on your systems.
How quickly can I see results after starting a scan?
The platform is designed for speed and immediate insight. Upon initiating a scan, Threat Watch begins processing data from its continuously updated intelligence feeds. You can start seeing initial results, such as identified compromised credentials or breached accounts, very quickly, allowing for rapid assessment of your critical security health categories.
Is Threat Watch suitable for a small business without a dedicated security team?
Absolutely. Threat Watch is built for organizations of all sizes. Its centralized dashboard and clear, prioritized findings are designed to be actionable even for users without deep cybersecurity expertise. Small businesses can use it to understand their external risk exposure, take simple corrective actions like password changes, and significantly improve their security posture.
How does Threat Watch help in preventing a cyber attack?
Threat Watch enables prevention by focusing on pre-attack indicators. By identifying stolen credentials, phishing setups, and exposed assets before they are actively weaponized by attackers, the platform provides a crucial window for remediation. This allows you to reset passwords, take down phishing sites, and patch vulnerabilities proactively, closing doors that attackers would otherwise use to gain entry.
Zignt FAQ
What makes Zignt different from other e-signature tools?
Zignt distinguishes itself by eliminating per-signature fees, allowing users to send unlimited documents without worrying about additional costs. This scalable pricing model is ideal for businesses of all sizes, providing significant savings and predictability.
Is Zignt secure for handling sensitive documents?
Yes, Zignt employs bank-grade security measures, including 256-bit SSL/TLS encryption for documents in transit and at rest. Additionally, it complies with international legal standards, ensuring that all signatures are legally enforceable.
Can I invite team members to collaborate on contracts?
Absolutely! Zignt allows users to invite unlimited team members to collaborate on contract preparation and sending. You can also control permissions for each member, ensuring that sensitive information is accessible only to authorized personnel.
How does Zignt track contract renewals?
Zignt's AI technology automatically scans contracts to identify renewal dates and significant milestones. It sends smart reminders to users, helping them stay organized and proactive in managing their contract renewals without manual effort.
Alternatives
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence platform that provides businesses with a real-time, actionable view of their external digital security posture. It automates the discovery of vulnerabilities like exposed credentials and dark web exposures, delivering a clear cyber health score to guide risk management. Users explore alternatives for various reasons, including budget constraints, specific feature requirements not covered by a single platform, or the need to integrate with an existing security tech stack. The search often stems from a desire to compare capabilities, pricing models, or scalability for different organizational sizes. When evaluating alternatives, key considerations should include the scope of external attack surface monitoring, the depth and speed of threat intelligence, the clarity of risk prioritization, and the overall value relative to cost. The goal is to find a solution that effectively transforms complex threat data into proactive, defensible actions.
Zignt Alternatives
Zignt is a comprehensive electronic signature and contract management platform designed to enhance business workflows through automation and security. By offering features like reusable templates and AI-powered renewal management, Zignt streamlines the traditionally convoluted process of contract creation, sending, and tracking. This all-in-one solution appeals to a wide range of businesses, from startups to established enterprises, by ensuring legal compliance while reducing manual effort. Users often seek alternatives to Zignt due to various reasons such as pricing, specific feature requirements, or compatibility with existing platforms. When selecting an alternative, it's essential to consider factors such as user-friendliness, security measures, pricing models, and the ability to integrate with other tools. An ideal alternative should not only meet current needs but also scale with future business growth.
