Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
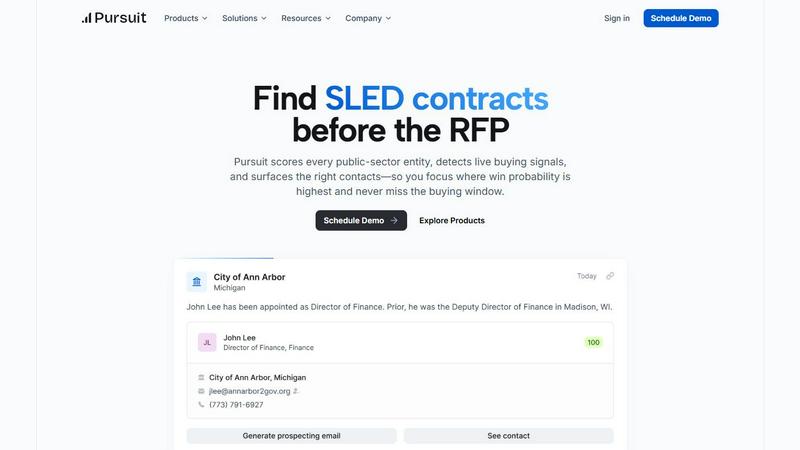
Pursuit
Pursuit uses AI to uncover and score public sector sales opportunities well before RFPs are released.
Last updated: February 28, 2026
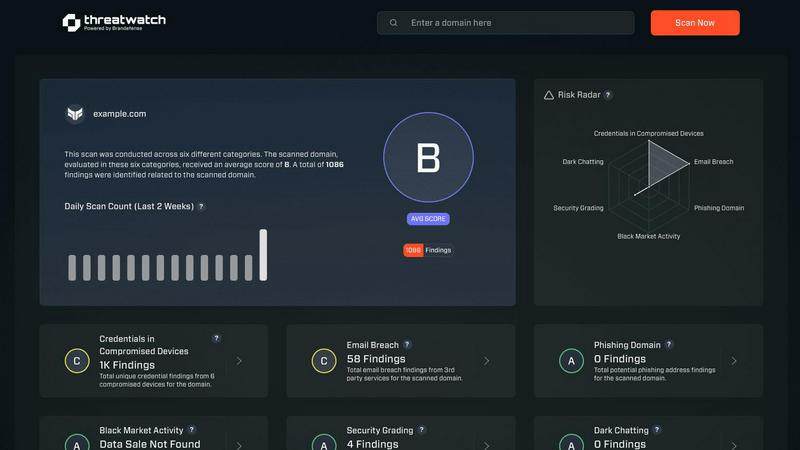
Threat Watch
Instantly assess your cybersecurity health with a free scan for critical vulnerabilities.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Intelligence
Pursuit surfaces buying signals 6 to 18 months before RFPs go live, allowing your team to position itself as the incumbent rather than an outsider. This early insight into procurement activities enables proactive engagement with potential clients.
Centralized Data Monitoring
The platform continuously monitors and analyzes data from over 90,000 public entities, providing a comprehensive view of buying signals, procurement cycles, and critical budget information that informs sales strategies.
Seamless CRM Integration
With native integrations to Salesforce and HubSpot, Pursuit ensures that data flows directly into your existing stack, eliminating manual data entry and enhancing the accuracy of your sales intelligence.
Role-Specific Functionality
Pursuit is designed with deep functionality for every role within your go-to-market team, from Revenue Operations to Account Executives, ensuring that every team member has the tools they need to succeed in their specific tasks.
Threat Watch
Comprehensive Cyber Health Assessment
Threat Watch provides a unified, real-time dashboard that evaluates an organization's overall cybersecurity posture. It systematically scans and analyzes multiple critical security categories, delivering a clear and consolidated view of risks. This holistic assessment transforms disparate data points into an understandable security health score, enabling teams to quickly grasp their current standing and identify areas requiring immediate attention.
Automated Compromised Credentials Detection
The platform continuously monitors data breaches and leak repositories to identify if employee credentials, such as emails and passwords, have been exposed. This automated surveillance extends beyond public databases to include dark web sources, ensuring that stolen login information is flagged promptly. This allows security teams to enforce password resets and implement multi-factor authentication before accounts can be abused.
Breached Account and Phishing Risk Monitoring
Threat Watch actively tracks instances where corporate email accounts appear in known data breaches or are being used in phishing campaigns. It identifies if company domains are being spoofed or impersonated, alerting organizations to active phishing threats targeting their employees or customers. This early warning system is crucial for preempting social engineering attacks and protecting brand reputation.
External Attack Surface Analysis
The solution automates the discovery and assessment of an organization's externally visible digital assets, including domains, IP addresses, and associated services. It identifies misconfigurations, outdated software, and unintended exposures that could serve as entry points for attackers. This continuous mapping provides a clear picture of the external attack surface, enabling proactive hardening of defenses.
Use Cases
Pursuit
Revenue Operations Efficiency
Revenue operations teams can leverage Pursuit to achieve 94% data accuracy through continuous enrichment, significantly reducing the time spent on data management and allowing teams to focus on strategic initiatives.
Sales Leadership Insights
Sales leaders can use Pursuit to identify which sales representatives are working on which signals, analyze territory coverage gaps, and forecast with confidence using real-time SLED buying indicators to drive team performance.
Targeted Marketing Campaigns
Marketing teams can build account-based marketing (ABM) campaigns centered around real buying signals, such as budget approvals and contract expirations, thus improving campaign effectiveness and conversion rates.
Enhanced Account Executive Preparedness
Account executives can utilize Pursuit’s Chrome extension for instant meeting preparation, gaining insights into the incumbent, contract values, and procurement details before every call, leading to improved win rates.
Threat Watch
Proactive Risk Management for IT Security Teams
Security operations and IT teams use Threat Watch to shift from a reactive, alert-driven model to a proactive risk management stance. By having a centralized, real-time view of external threats like compromised credentials and dark web exposures, teams can prioritize remediation efforts based on actual risk, allocate resources more effectively, and prevent incidents before they escalate into full-scale breaches.
Compliance and Audit Readiness
Compliance officers and auditors leverage the platform to demonstrate due diligence in monitoring third-party and digital risks. The comprehensive reports and historical data provided by Threat Watch serve as evidence of continuous security monitoring, helping organizations meet regulatory requirements for data protection, risk assessment, and incident response preparedness across various frameworks.
Executive and Board-Level Security Reporting
Business leaders and board members utilize Threat Watch's clear, dashboard-driven insights to understand the organization's cyber risk in business terms. The platform translates technical vulnerabilities into prioritized business risks, facilitating informed decision-making regarding security investments and providing assurance that the digital attack surface is being actively managed.
Vendor and Third-Party Risk Assessment
Organizations extend their security monitoring to assess the cyber health of key partners and vendors. By analyzing the external digital footprint of third parties, businesses can identify if a supplier's breached data or exposed assets pose a downstream risk to their own network, enabling more informed vendor risk management and contract discussions.
Overview
About Pursuit
Pursuit is an advanced AI-powered sales intelligence platform tailored specifically for businesses engaged in selling to state, local, and educational (SLED) government entities. By transforming the often intricate and opaque public-sector sales process into a streamlined, data-driven operation, Pursuit equips sales, business development, and sales operations teams with critical insights. The platform caters to government technology vendors, SaaS companies, and contractors, offering unparalleled visibility into a vast public sector market encompassing over 110,000 entities. Pursuit's core mission is to eliminate friction in the sales process by enabling companies to focus their efforts on high-probability contract opportunities and to identify crucial buying signals effectively. By continuously monitoring and analyzing data from diverse public entities, Pursuit evaluates procurement likelihood, detects live buying intent from various sources, and provides accurate contact information for the entire buying committee. This centralized intelligence empowers sales teams to transition from reactive RFP chasing to proactive and strategic pipeline generation, ultimately enhancing their chances of winning contracts.
About Threat Watch
Threat Watch is a unified cybersecurity intelligence platform designed to provide organizations with a comprehensive and real-time view of their digital security posture. It functions as a centralized hub for cyber health assessment, continuously analyzing an organization's external digital footprint, assets, vulnerabilities, and exposures. The platform's core mission is to transform complex, fragmented threat data into a clear, actionable picture of risk. By automating the discovery and assessment of critical security categories, Threat Watch empowers IT security teams, compliance officers, and business leaders to move from reactive defense to proactive risk management. Its primary value proposition lies in its speed and clarity; it rapidly identifies issues like compromised credentials, breached accounts, phishing risks, and dark web exposures, allowing teams to prioritize and mitigate threats faster than traditional manual methods. It is ideally suited for businesses of all sizes seeking to understand their external attack surface and strengthen their defenses against evolving cyber threats. The platform's "Uncover your Cyber Security Health, Fast!" approach delivers immediate insights, enabling organizations to take swift, informed action to secure their digital perimeter.
Frequently Asked Questions
Pursuit FAQ
What is Pursuit?
Pursuit is an AI-powered sales intelligence platform that provides businesses selling to SLED entities with critical insights and data-driven tools to enhance their sales processes and contract win rates.
How does Pursuit help in identifying contract opportunities?
Pursuit identifies buying signals 6 to 18 months prior to RFPs going live, enabling sales teams to engage with potential clients well before formal procurement processes begin, thereby increasing their chances of success.
Can Pursuit integrate with my existing CRM?
Yes, Pursuit offers native integrations with major CRM platforms like Salesforce and HubSpot, ensuring seamless data flow and enhancing the efficiency of your sales operations.
What types of organizations can benefit from Pursuit?
Pursuit is designed for government technology vendors, SaaS companies, and contractors that sell to state, local, and educational entities, providing them with the intelligence needed to navigate complex procurement processes.
Threat Watch FAQ
What does Threat Watch actually scan and monitor?
Threat Watch performs a non-intrusive external scan of your organization's digital footprint. It monitors for compromised employee credentials in data breaches, detects corporate accounts involved in phishing schemes, identifies exposed company data on the dark web, and analyzes publicly accessible assets for vulnerabilities. It does not require internal network access or agents installed on your systems.
How quickly can I see results after starting a scan?
The platform is designed for speed and immediate insight. Upon initiating a scan, Threat Watch begins processing data from its continuously updated intelligence feeds. You can start seeing initial results, such as identified compromised credentials or breached accounts, very quickly, allowing for rapid assessment of your critical security health categories.
Is Threat Watch suitable for a small business without a dedicated security team?
Absolutely. Threat Watch is built for organizations of all sizes. Its centralized dashboard and clear, prioritized findings are designed to be actionable even for users without deep cybersecurity expertise. Small businesses can use it to understand their external risk exposure, take simple corrective actions like password changes, and significantly improve their security posture.
How does Threat Watch help in preventing a cyber attack?
Threat Watch enables prevention by focusing on pre-attack indicators. By identifying stolen credentials, phishing setups, and exposed assets before they are actively weaponized by attackers, the platform provides a crucial window for remediation. This allows you to reset passwords, take down phishing sites, and patch vulnerabilities proactively, closing doors that attackers would otherwise use to gain entry.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered sales intelligence platform designed specifically for businesses targeting state, local, and educational (SLED) government entities. It enhances the public sector sales process by providing data-driven insights, allowing sales teams to identify and pursue opportunities with the highest probability of success. Users often seek alternatives to Pursuit for various reasons, including pricing concerns, specific feature requirements, or integration needs with existing tools. When choosing an alternative, it's crucial to consider factors like the comprehensiveness of the data provided, the effectiveness of the AI in identifying opportunities, and the level of support for your sales team. Additionally, evaluate how well the alternative integrates with your current systems and how it aligns with your overall sales strategy and objectives.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence platform that provides businesses with a real-time, actionable view of their external digital security posture. It automates the discovery of vulnerabilities like exposed credentials and dark web exposures, delivering a clear cyber health score to guide risk management. Users explore alternatives for various reasons, including budget constraints, specific feature requirements not covered by a single platform, or the need to integrate with an existing security tech stack. The search often stems from a desire to compare capabilities, pricing models, or scalability for different organizational sizes. When evaluating alternatives, key considerations should include the scope of external attack surface monitoring, the depth and speed of threat intelligence, the clarity of risk prioritization, and the overall value relative to cost. The goal is to find a solution that effectively transforms complex threat data into proactive, defensible actions.
